The Sneaky2FA phishing-as-a-service (PhaaS) equipment has added browser-in-the-browser (BitB) capabilities which are utilized in assaults to steal Microsoft credentials and energetic classes.
Sneaky2FA is a broadly used PhaaS platform proper now, alongside Tycoon2FA and Mamba2FA, all concentrating on primarily Microsoft 365 accounts.
The equipment was recognized for its SVG-based assaults and attacker-in-the-middle (AitM) techniques, the place the authentication course of is proxied to the legit service via a phishing web page that relays legitimate session tokens to the attackers.
In keeping with a report from Push Safety, Sneaky2FA has now added a BitB pop-up that mimics a legit Microsoft login window. So as to add to the deception, the faux sign-in web page adjusts dynamically to the sufferer’s OS and browser.
An attacker stealing credentials and energetic session tokens can authenticate to the sufferer’s accoun,t even when the two-factor authentication (2FA) safety is energetic.
BitB is a phishing method devised by researcher mr.d0x in 2022 and has since been adopted by menace actors for actual assaults concentrating on Fb and Steam accounts, amongst different companies.
In the course of the assault, customers touchdown on an attacker-controlled webpage see a faux browser pop-up window with a login type.
The template for the pop-up is an iframe that mimics the authentication type of legit companies and may be custom-made with a selected URL and window title.
As a result of the faux window shows a URL bar with the focused service’s official area handle, it appears like a reliable OAuth pop-up.
Within the case of Sneaky2FA, the sufferer opens a phishing hyperlink on ‘previewdoc[.]com’ and goes via a Cloudflare Turnstile bot test earlier than they’re prompted to register with Microsoft to view a doc.
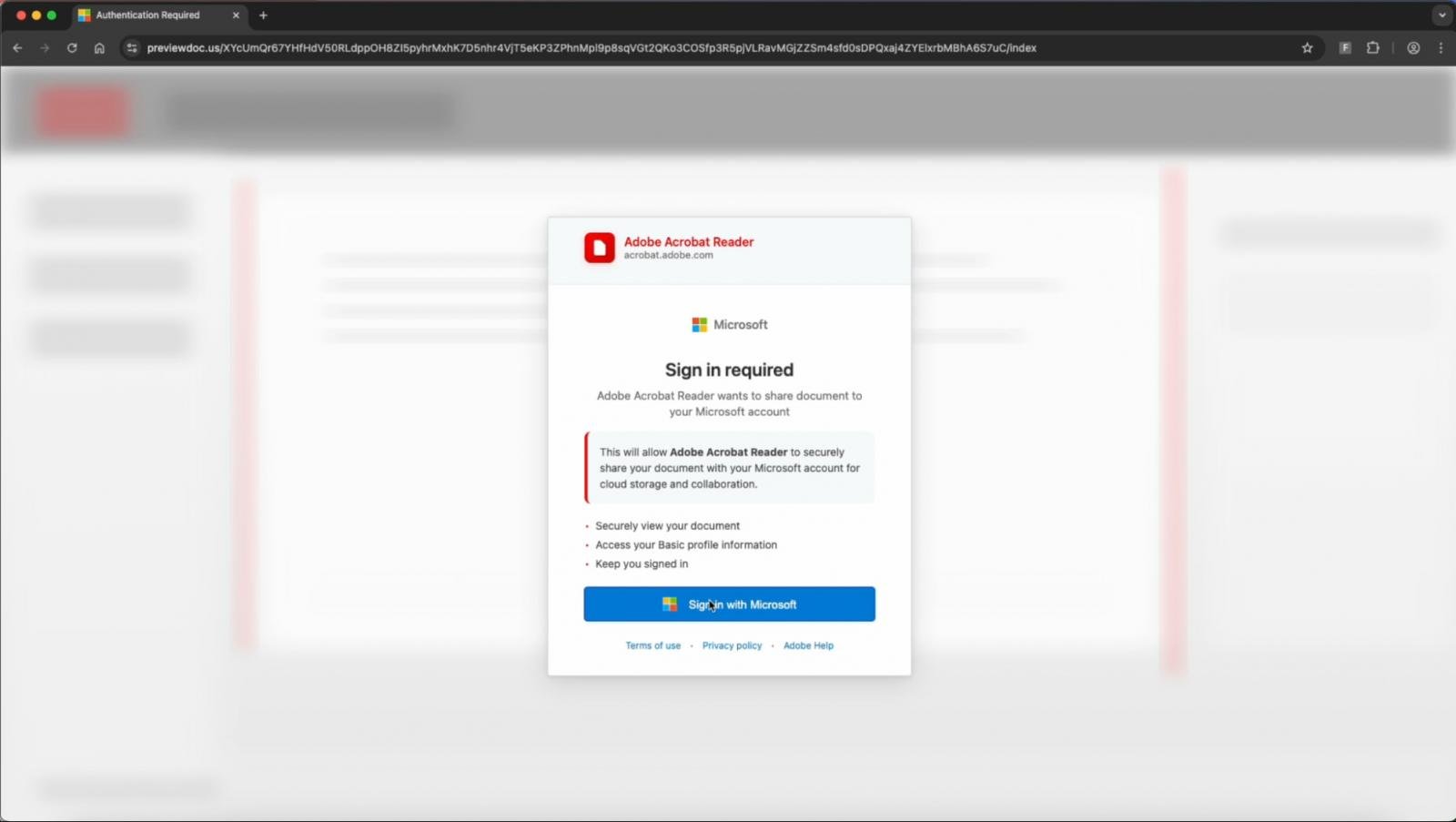
Supply: Push Safety
If the “Check in with Microsoft” possibility is clicked, the faux BitB window is rendered, that includes a faux Microsoft URL bar, resized and styled appropriately for Edge on Home windows or Safari on macOS.
Contained in the faux pop-up, Sneaky2FA hundreds its reverse-proxy Microsoft phishing web page, so it leverages the actual login circulation to steal each the account credentials and the session token by way of its AitM system.
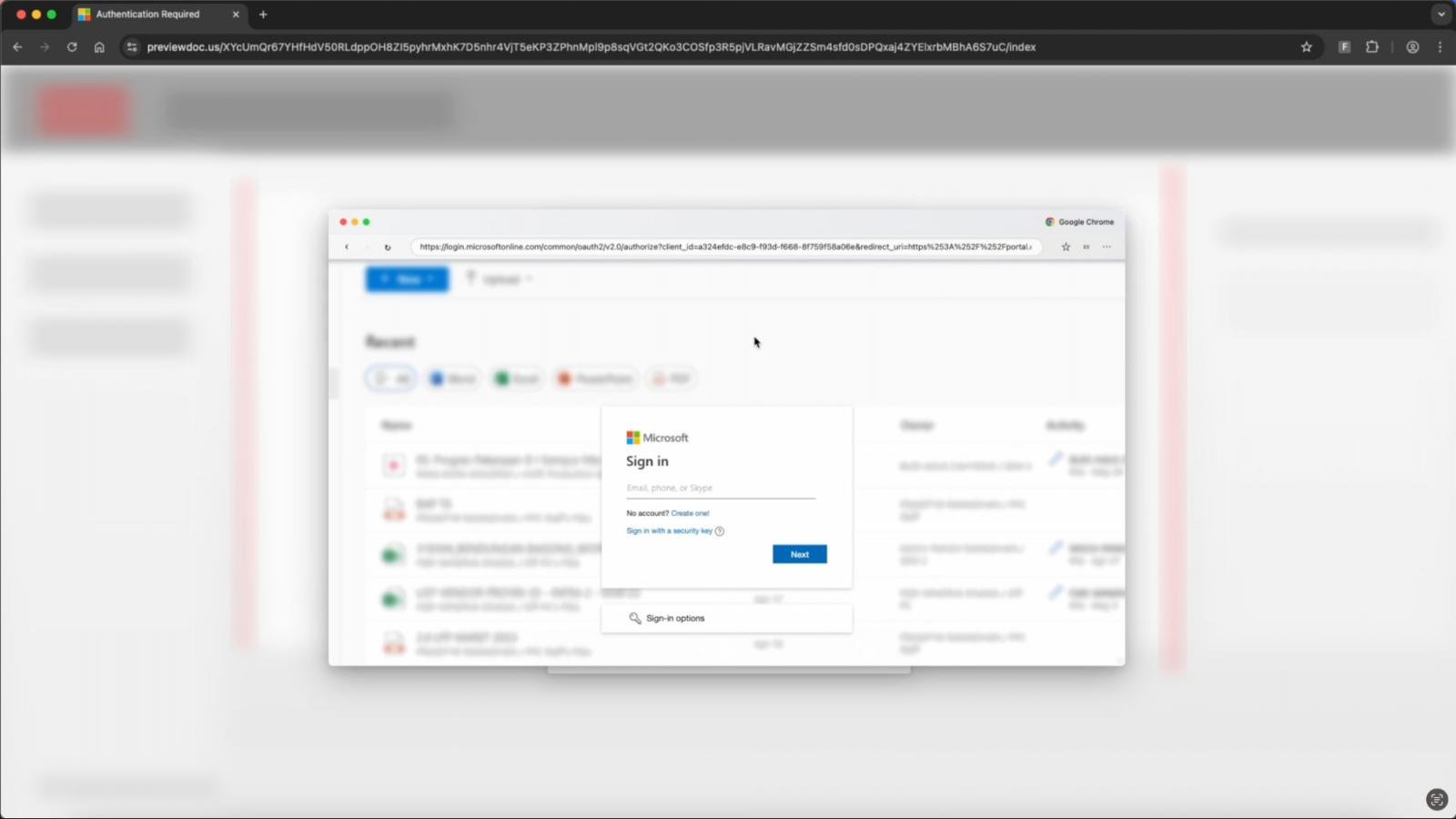
Supply: Push Safety
Basically, BitB is used as a beauty deception layer on high of Sneaky2FA’s current AitM capabilities, including extra realism to the assault chain.
The phishing equipment additionally makes use of conditional loading, sending bots and researchers to a benign web page as an alternative.
Push Safety experiences that these phishing websites are crafted with evasion in thoughts, they usually’re unlikely to set off warnings when visited.
“The HTML and JavaScript of Sneaky2FA pages are closely obfuscated to evade static detection and pattern-matching, equivalent to breaking apart UI textual content with invisible tags, embedding background and interface parts as encoded photographs as an alternative of textual content, and different modifications which are invisible to the person, however make it laborious for scanning instruments to fingerprint the web page,” clarify the researchers.
One option to decide if a pop-up login type is genuine is to attempt to drag it outdoors the unique browser window. This isn’t doable with an iframe as a result of it’s linked to its dad or mum window.
Moreover, a legit pop-up seems within the taskbar as a separate browser occasion.
Help for BitB has been seen with one other PhaaS service known as Raccoon0365/Storm-2246, which was just lately disrupted by Microsoft and Cloudflare after stealing hundreds of Microsoft 365 credentials.
It is funds season! Over 300 CISOs and safety leaders have shared how they’re planning, spending, and prioritizing for the yr forward. This report compiles their insights, permitting readers to benchmark methods, determine rising developments, and examine their priorities as they head into 2026.
Find out how high leaders are turning funding into measurable impression.



