A Russian-linked marketing campaign delivers the StealC V2 info stealer malware by way of malicious Blender information uploaded to 3D mannequin marketplaces like CGTrader.
Blender is a strong open-source 3D creation suite that may execute Python scripts for automation, customized consumer interface panels, add-ons, rendering processes, rigging instruments, and pipeline integration.
If the Auto Run characteristic is enabled, when a consumer opens a personality rig, a Python script can mechanically load the facial controls and customized UI panels with the required buttons and sliders.
Regardless of the potential for abuse, customers typically activate the Auto Run choice for comfort.
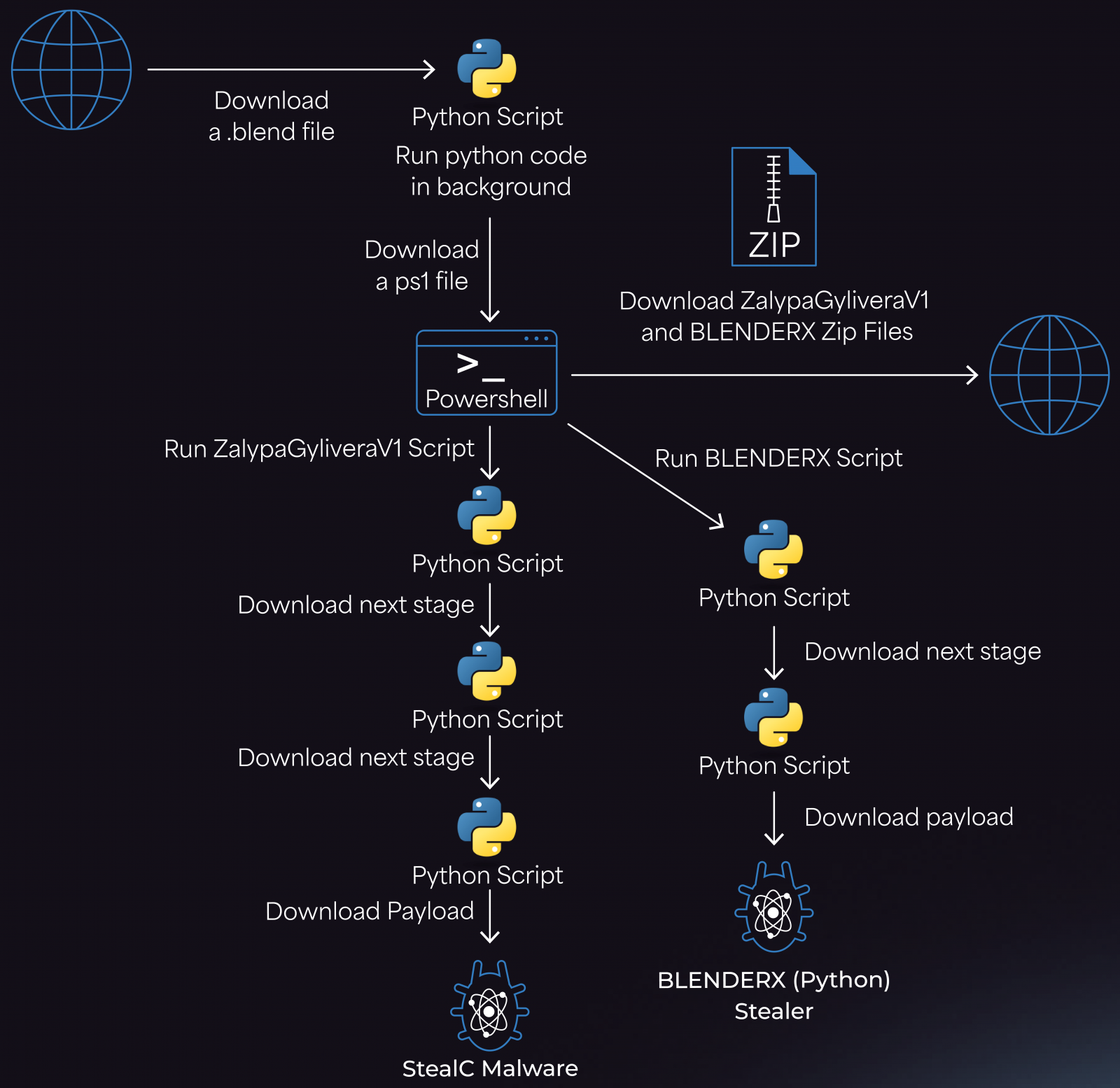
Researchers at cybersecurity firm Morphisec noticed assaults utilizing malicious .mix information with embedded Python code that fetches a malware loader from a Cloudflare Staff area.
Supply: Morphisec
The loader then fetches a PowerShell script that retrieves two ZIP archives, ZalypaGyliveraV1 and BLENDERX, from attacker-controlled IPs.
The archives unpack into the %TEMP% folder and drop LNK information within the Startup listing for persistence. Subsequent, they deploy two payloads, the StealC infostealer and an auxiliary Python stealer, possible used for redundancy.
Supply: Morphisec
Morphisec researchers report that the StealC malware used on this marketing campaign was the most recent variant of the second main model of the malware that was analyzed by Zscaler researchers earlier this yr.
The newest StealC has expanded its data-stealing capabilities and helps exfiltration from:
- 23+ browsers, with server-side credential decryption and compatibility with Chrome 132+
- 100+ cryptocurrency pockets browser extensions and 15+ cryptocurrency pockets apps
- Telegram, Discord, Tox, Pidgin, VPN shoppers (ProtonVPN, OpenVPN), and mail shoppers (Thunderbird)
- Up to date UAC bypass mechanism
Regardless of the malware being documented since 2023, subsequent releases seem to stay elusive for anti-virus merchandise. Morphisec feedback that no safety engine on VirusTotal detected the StealC variant they analyzed.
Provided that 3D mannequin marketplaces can’t scrutinize the code in user-submitted information, Blender customers are suggested to train warning when utilizing information sourced from such platforms and may contemplate disabling the auto-execution of code.
You are able to do this from Blender > Edit > Preferences > uncheck the ‘Auto Run Python Scripts’ choice.
3D belongings ought to be handled like executable information, and customers ought to solely belief publishers with a confirmed report. For the whole lot else, it is strongly recommended to make use of sandboxed environments for testing.
It is funds season! Over 300 CISOs and safety leaders have shared how they’re planning, spending, and prioritizing for the yr forward. This report compiles their insights, permitting readers to benchmark methods, determine rising developments, and evaluate their priorities as they head into 2026.
Learn the way prime leaders are turning funding into measurable influence.

.jpg)

