Your management staff is speaking about Generative AI. Your CIO has an AI-readiness initiative. The mandate from the highest is obvious: automate, innovate, and discover a aggressive edge with synthetic intelligence.
However you recognize the reality.
The crucial knowledge wanted to energy these AI initiatives is trapped in a 15-page scanned PDF from a brand new provider, a blurry picture of a invoice of lading, and an e-mail inbox overflowing with buy orders. The C-suite’s imaginative and prescient of an AI-powered future is colliding with the bottom reality of doc processing—and also you’re caught within the center.
This is not a novel downside. A surprising 77% of organizations admit their knowledge will not be prepared for AI, primarily as a result of it is locked on this actual form of info chaos. The largest hurdle to AI is not the accuracy of the mannequin; it is the enter.
This text is not about AI hype. It is concerning the foundational work of knowledge seize that makes all of it potential. We’ll break down learn how to resolve the enter downside, transferring from the brittle, template-based instruments of the previous to an clever system that delivers clear, structured, AI-ready knowledge with 95%+ accuracy.
The muse: Defining the what and why of information seize
To resolve an issue, we should first outline it accurately. The problem of managing paperwork has advanced far past easy paperwork. It’s a strategic knowledge downside that immediately impacts effectivity, price, and an organization’s means to innovate.
Core definitions and terminology
Data seize is the method of extracting info from unstructured or semi-structured sources and changing it right into a structured, machine-readable format.
To be exact, knowledge exists in three major varieties:
- Unstructured knowledge: Info with no predefined knowledge mannequin, such because the textual content in an e-mail, the physique of a authorized contract, or a picture.
- Semi-structured knowledge: Loosely organized knowledge that comprises tags or markers to separate semantic parts however doesn’t match a inflexible database mannequin. Invoices and buy orders are traditional examples.
- Structured knowledge: Extremely organized knowledge that matches neatly right into a tabular format, like a database or a spreadsheet.
The objective of information seize is to rework unstructured and semi-structured inputs into structured outputs (like Markdown, JSON, or CSV) that can be utilized by different enterprise software program. In technical and tutorial circles, this complete course of is also known as Doc Parsing, whereas in analysis circles, it’s generally often known as Digital Knowledge Seize (EDC).
The strategic crucial: Why knowledge seize is a enterprise precedence
Efficient knowledge seize is not a back-office optimization; it’s the foundational layer for strategic initiatives, resembling digital transformation and AI-powered workflows.
Two realities of the fashionable enterprise drive this urgency:
- The info explosion: Over 80% of all enterprise knowledge is unstructured, locked away in paperwork, photographs, and different hard-to-process codecs, in line with a number of trade analyses.
- Fragmented know-how: This info chaos is compounded by a sprawling and disconnected know-how stack. The common group makes use of greater than 10 totally different info administration programs (e.g., ERP, CRM, file sharing), and research report that over half of those programs have low or no interoperability, leading to remoted knowledge silos.
This disjointed setup crammed with info chaos—the place crucial knowledge is trapped in unstructured paperwork and unfold throughout disconnected programs—makes a unified view of enterprise operations unattainable. This similar fragmentation is the first cause that strategic AI initiatives fail.
Superior purposes like Retrieval-Augmented Era (RAG) are significantly susceptible. RAG programs are designed to reinforce the accuracy and relevance of huge language fashions by retrieving info from a various array of exterior knowledge sources, together with databases, APIs, and doc repositories. The reliability of a RAG system’s output is solely depending on the standard of the information it could entry.
If the information sources are siloed, inconsistent, or incomplete, the RAG system inherits these flaws. It can retrieve fragmented info, resulting in inaccurate solutions, hallucinations, and in the end, a failed AI mission. Because of this fixing the foundational knowledge seize and structuring downside is the non-negotiable first step earlier than any profitable enterprise AI deployment.
The central battle: Handbook vs. automated processing
The choice of learn how to carry out knowledge seize has a direct and important influence on an organization’s backside line and operational capability.
- Handbook knowledge seize: This conventional strategy includes human operators keying in knowledge. It’s basically unscalable. It’s notoriously gradual and liable to human error, with noticed error charges starting from 1% to 4%. A 2024 report from Ardent Companions discovered the typical all-inclusive price to course of a single bill manually is $17.61.
- Automated knowledge seize: This contemporary strategy makes use of know-how to carry out the identical duties. Clever options ship 95%+ accuracy, course of paperwork in seconds, and scale to deal with tens of millions of pages with no proportional improve in price. The identical Ardent Companions report discovered that full automation reduces the per-invoice processing price to beneath $2.70—an 85% lower.
The selection is not about choice; it is about viability. In an ecosystem that calls for pace, accuracy, and scalability, automation is the logical path ahead.
The evolution of seize know-how: From OCR to IDP
The know-how behind automated knowledge seize has advanced considerably. Understanding this evolution is essential to avoiding the pitfalls of outdated instruments and appreciating the capabilities of recent programs.
The previous guard: Why conventional OCR fails
The primary wave of automation was constructed on a number of core applied sciences, with Optical Character Recognition (OCR) at its middle. OCR converts photographs of typed textual content into machine-readable characters. It was usually supplemented by:
- Clever Character Recognition (ICR): An extension designed to interpret handwritten textual content.
- Barcodes & QR Codes: Strategies for encoding knowledge into visible patterns for fast scanning.
The elemental flaw of those early instruments was their reliance on mounted templates and inflexible guidelines. This template-based strategy requires a developer to manually outline the precise coordinates of every knowledge discipline for a particular doc structure.
That is the know-how that created widespread skepticism about automation, as a result of it constantly fails in dynamic enterprise environments for a number of key causes:
- It’s inefficient: A vendor shifting their emblem, including a brand new column, and even barely altering a font can break the template, inflicting the automation to fail and requiring pricey IT intervention.
- It doesn’t scale: Creating and sustaining a novel template for each vendor, buyer, or doc variation is operationally unattainable for any enterprise with a various set of suppliers or purchasers.
- It lacks intelligence: It struggles to precisely extract knowledge from complicated tables, differentiate between visually related however contextually totally different fields (e.g., Bill Date vs. Due Date), or reliably learn different handwriting.
In the end, this strategy compelled groups to spend extra time managing and fixing damaged templates than they saved on knowledge entry, main many to desert the know-how altogether.
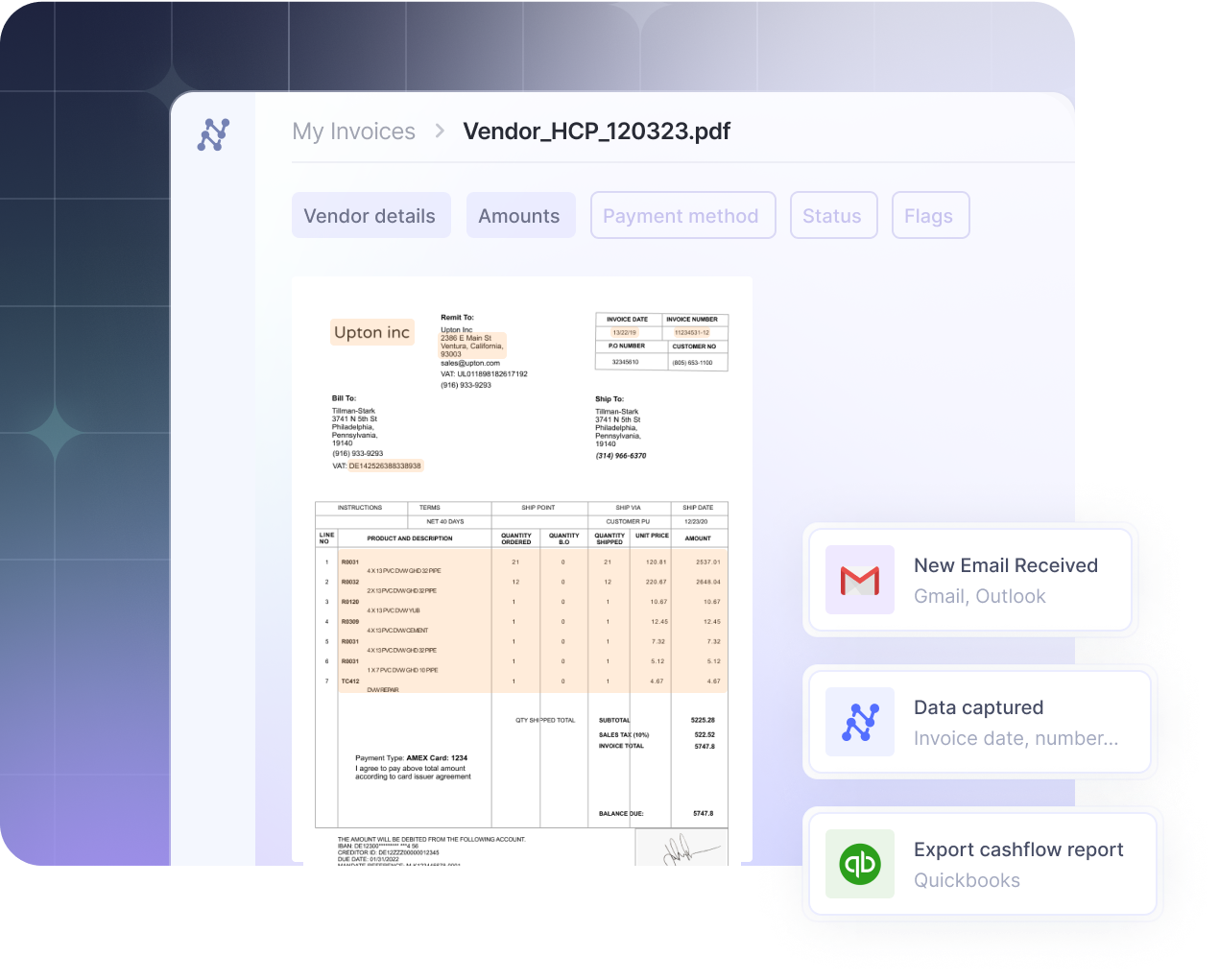
The trendy answer: Clever Doc Processing (IDP)
Clever Doc Processing (IDP) is the AI-native successor to conventional OCR. As an alternative of counting on templates, IDP platforms use a mixture of AI, machine studying, and pc imaginative and prescient to know a doc’s content material and context, very similar to a human would.
The core engine driving fashionable IDP is commonly a kind of AI often known as a Imaginative and prescient-Language Mannequin (VLM). A VLM can concurrently perceive and course of each visible info (the structure, construction, and pictures on a web page) and textual knowledge (the phrases and characters). This twin functionality is what makes fashionable IDP programs basically totally different and vastly extra highly effective than legacy OCR.
A key technical differentiator on this course of is Doc Structure Evaluation (DLA). Earlier than trying to extract any knowledge, an IDP system’s VLM first analyzes the doc’s general visible construction to determine headers, footers, paragraphs, and tables. This means to fuse visible and semantic info is why IDP platforms, resembling Nanonets, can precisely course of any doc format from day one, without having a pre-programmed template. That is usually described as a “Zero-Shot” or “Immediate Studying” functionality, the place the mannequin learns and adapts to new codecs on the fly.
The efficiency leap enabled by this AI-driven strategy is immense. A 2024 examine centered on transcribing complicated handwritten historic paperwork—a activity far more difficult than processing typical enterprise invoices—discovered that fashionable multimodal LLMs (the engine behind IDP) had been 50 instances quicker and 1/fiftieth the fee of specialised legacy software program. Crucially, they achieved state-of-the-art accuracy “out of the field” with out the intensive, document-specific fine-tuning that older programs required to perform reliably.
Adjoining applied sciences: The broader automation ecosystem
IDP is a specialised software for turning unstructured doc knowledge into structured info. It usually works in live performance with different automation applied sciences to create an precise end-to-end workflow:
- Robotic Course of Automation (RPA): RPA bots act as digital employees that may orchestrate a workflow. For instance, an RPA bot might be programmed to observe an e-mail inbox, obtain an bill attachment, ship it to an IDP platform for knowledge extraction, after which use the structured knowledge returned by the IDP system to finish a activity in an accounting utility.
- Change Knowledge Seize (CDC): Whereas IDP handles unstructured paperwork, CDC is a extra technical, database-level technique for capturing real-time modifications (inserts, updates, deletes) to structured knowledge. It is a crucial know-how for contemporary, event-driven architectures the place programs like microservices want to remain synchronized immediately.
Collectively, these applied sciences type a complete automation toolkit, with IDP serving the important position of changing the chaotic world of unstructured paperwork into the clear, dependable knowledge that each one different programs rely upon.
The operational blueprint: How knowledge seize works in observe
Trendy clever knowledge seize will not be a single motion however a scientific, multi-stage pipeline. Understanding this operational blueprint is important for transferring from chaotic, guide processes to streamlined, automated workflows. The complete course of, from doc arrival to remaining knowledge supply, is designed to make sure accuracy, implement enterprise guidelines, and allow true end-to-end automation.
The trendy knowledge seize pipeline
An efficient IDP system operates as a steady workflow. This pipeline is commonly often known as a modular system for doc parsing and aligns with the information administration lifecycle required for superior AI purposes.
Step 1: Knowledge ingestion
The method begins with getting paperwork into the system. A versatile platform should assist a number of ingestion channels to deal with info from any supply, together with:
- Electronic mail forwarding: Routinely processing invoices and different paperwork despatched to a devoted e-mail tackle (e.g., invoices@firm.com).
- Cloud storage integration: Watching and mechanically importing information from cloud folders in Google Drive, OneDrive, Dropbox, or SharePoint.
- API uploads: Permitting direct integration with different enterprise purposes to push paperwork into the seize workflow programmatically.
Step 2: Pre-processing and classification
As soon as ingested, the system prepares the doc for correct extraction. This includes automated picture enhancement, resembling correcting skew and eradicating noise from scanned paperwork.
Critically, the AI then classifies the doc. Utilizing visible and textual evaluation, it determines the doc sort—immediately distinguishing a US-based W-2 type from a UK-based P60, or an bill from a invoice of lading—and routes it to the suitable specialised mannequin for extraction.
Step 3: AI-powered extraction
That is the core seize step. As established, IDP makes use of VLMs to carry out Doc Structure Evaluation, understanding the doc’s construction earlier than extracting knowledge fields. This enables it to seize info precisely:
- Headers and footers
- Line objects from complicated tables
- Handwritten notes and signatures
This course of works immediately on any doc format, eliminating the necessity for creating or sustaining templates.
Step 4: Validation and high quality management
Extracted knowledge is ineffective if it’s not correct. That is probably the most crucial step for reaching belief and enabling excessive charges of straight-through processing (STP). Trendy IDP programs validate knowledge in real-time by way of a sequence of checks:
- Enterprise rule enforcement: Making use of customized guidelines, resembling flagging an bill if the total_amount doesn’t equal the sum of its line_items plus tax.
- Database matching: Verifying extracted knowledge in opposition to an exterior system of document. This might contain matching a vendor’s VAT quantity in opposition to the EU’s VIES database, guaranteeing an bill complies with PEPPOL e-invoicing requirements prevalent in Europe and ANZ, or validating knowledge in accordance with privateness laws like GDPR and CCPA.
- Exception dealing with: Solely paperwork that fail these automated checks are flagged for human evaluation. This exception-only workflow permits groups to focus their consideration on the small share of paperwork that require it.
This validation stage aligns with the Confirm step within the RAG pipeline, which confirms knowledge high quality, completeness, consistency, and uniqueness earlier than downstream AI programs use it.
Step 5: Knowledge integration and supply
The ultimate step is delivering the clear, verified, and structured knowledge to the enterprise programs the place it’s wanted. The info is usually exported in a standardized format, resembling JSON or CSV, and despatched on to its vacation spot by way of pre-built connectors or webhooks, thereby closing the loop on automation.
Construct vs. purchase: The position of open supply and foundational fashions
For organizations with deep technical experience, a construct strategy utilizing open-source instruments and foundational fashions is an choice. A staff may assemble a pipeline utilizing foundational libraries like Tesseract or PaddleOCR for the preliminary textual content recognition.
A extra superior start line can be to make use of a complete open-source library like our personal DocStrange. This library goes far past fundamental OCR, offering a robust toolkit to extract and convert knowledge from almost any doc sort—together with PDFs, Phrase paperwork, and pictures—into clear, LLM-ready codecs like Markdown and structured JSON. With choices for 100% native processing, it additionally affords a excessive diploma of privateness and management.
For the intelligence layer, a staff may then combine the output from DocStrange with a general-purpose mannequin, resembling GPT-5 or Claude 4.1, by way of an API. This requires subtle immediate engineering to instruct the mannequin to search out and construction the precise knowledge fields wanted for the enterprise course of.
Nevertheless, this construct path carries important overhead. It requires a devoted engineering staff to:
- Handle the whole pipeline: Stitching the elements collectively and constructing all the mandatory pre-processing, post-processing, and validation logic.
- Construct a person interface: That is probably the most crucial hole. Open-source libraries present no front-end for enterprise customers (like AP clerks) to handle the inevitable exceptions, making a everlasting dependency on builders for each day operations.
- Deal with infrastructure and upkeep: Managing dependencies, mannequin updates, and the operational price of working the pipeline at scale.
A purchase answer from an IDP platform, resembling Nanonets’ business providing, productizes this complete complicated workflow. It packages the superior AI, a user-friendly interface for exception dealing with, and pre-built integrations right into a managed, dependable, and scalable service.
After extraction: The mixing ecosystem
Knowledge seize doesn’t exist in a vacuum. Its major worth is unlocked by its means to feed different core enterprise programs and break down info silos. Like we mentioned earlier, the largest problem is the dearth of interoperability between these programs.
An clever knowledge seize platform acts as a common translator, making a central level of management for unstructured knowledge and feeding clear info to:
- ERP and Accounting Programs: For totally automated accounts payable, platforms supply direct integrations with software program resembling SAP, NetSuite, QuickBooks, and Xero.
- Doc Administration Programs (DMS/ECM): For safe, long-term archival in platforms like SharePoint and OpenText.
- Robotic Course of Automation (RPA) Bots: Offering structured knowledge to bots from distributors like UiPath or Automation Wherever to carry out rule-based duties.
- Generative AI/RAG Pipelines: Delivering clear, verified, and structured knowledge is the non-negotiable first step to constructing a dependable inner data base for AI purposes.
The objective is to create a seamless move of data that allows true end-to-end course of automation, from doc arrival to remaining motion, with minimal to no human intervention.
The enterprise worth: ROI and purposes
The first worth of any know-how is its means to resolve concrete enterprise issues. For clever knowledge seize, this worth is demonstrated by way of measurable enhancements in price, pace, and knowledge reliability, which in flip assist strategic enterprise aims.
1. Measurable price discount
Probably the most important consequence of clever knowledge seize is the discount of operational prices. By minimizing the guide labor required for doc dealing with, organizations can obtain substantial financial savings. Actual-world implementation outcomes validate this monetary achieve.
For instance, UK-based Ascend Properties reported an 80% saving in processing prices after automating its upkeep invoices with Nanonets. This allowed the corporate to scale the variety of properties it managed from 2,000 to 10,000 with no proportional improve in administrative headcount.
2. Elevated processing velocity
Automating knowledge seize shrinks enterprise cycle instances from days to minutes. The Ardent Companions report additionally discovered that Finest-in-Class AP departments—these with excessive ranges of automation—course of and approve invoices in simply 3 days, in comparison with the 18-day common for his or her friends. This velocity improves money move administration and strengthens vendor relationships.
As a case instance, the worldwide paper producer Suzano Worldwide utilized Nanonets to scale back its buy order processing time from 8 minutes to only 48 seconds, a 90% discount in time that enabled quicker gross sales order creation of their SAP system.
3. Verifiable knowledge accuracy
Whereas guide knowledge entry is topic to error charges as excessive as 4%, fashionable IDP options constantly obtain 95%+ accuracy by eliminating human enter and utilizing AI for validation. This stage of information integrity is a crucial prerequisite for any strategic initiative that depends on knowledge, from enterprise intelligence to AI.
4. Strengthened safety and auditability
Automated programs create an immutable, digital audit path for each doc that’s processed. This supplies a transparent document of when a doc was obtained, what knowledge was extracted, and who accepted it. This auditability is important for assembly compliance with monetary laws just like the Sarbanes-Oxley Act (SOX) and knowledge privateness legal guidelines resembling GDPR in Europe and the CCPA in the US.
5. Scalable operations and workforce optimization
Clever knowledge seize decouples doc quantity from headcount. Organizations can deal with important progress without having to rent extra knowledge entry workers. Extra strategically, it permits for the optimization of the prevailing workforce. This aligns with a key development recognized in a 2023 McKinsey report, the place automation frees staff from repetitive guide and cognitive duties, permitting them to concentrate on higher-value work that requires superior technological, social, and emotional abilities.
Actual-world purposes throughout key industries
The worth of clever knowledge seize is realized within the tangible methods it streamlines core enterprise processes. Beneath are sensible knowledge extraction workflows for various industries, illustrating how info is reworked from disorganized paperwork into actionable knowledge in key enterprise programs.
a. Finance and Accounts Payable
That is among the many most typical and highest-impact use case.
The method earlier than IDP: Invoices arrive in an AP staff’s shared inbox. A clerk manually downloads every PDF, keys knowledge like vendor title, PO quantity, and line-item quantities into an Excel sheet, after which re-enters that very same knowledge into an ERP like NetSuite or SAP. This multi-step, guide course of is gradual, resulting in late fee charges and missed early-payment reductions.
The workflow with Clever Knowledge Seize:
- Invoices, together with these compliant with PEPPOL requirements within the EU and Australia or commonplace PDFs within the US, are mechanically fetched from a devoted inbox (e.g., invoices@firm.com).
- The IDP platform extracts and validates key knowledge—vendor title, bill quantity, line objects, and VAT/GST quantities.
- The system performs an automatic 2-way or 3-way match in opposition to buy orders and items receipt notes residing within the ERP system.
- As soon as validated, the information is exported immediately into the accounting system—QuickBooks, Xero, NetSuite, or SAP—to create a invoice that’s prepared for fee, usually with no human contact.
The end result: The AP automation answer supplier Augeo used this workflow to scale back the time its staff spent on bill processing from 4 hours per day to only half-hour—an 88% discount in guide work.
b. Logistics and Provide Chain
In logistics, pace and accuracy of documentation immediately influence supply instances and money move.
The method earlier than IDP: A driver completes a supply and will get a signed Proof of Supply (POD), usually a blurry picture or a multi-part carbon copy. A logistics coordinator on the again workplace manually deciphers the doc and keys the cargo ID, supply standing, and any handwritten notes right into a Transport Administration System (TMS). Delays or errors on this course of maintain up billing and cut back buyer visibility.
The workflow with Clever Knowledge Seize:
- Drivers add photographs of Payments of Lading (BOLs) and signed PODs by way of a cellular app immediately from the sector.
- The IDP system’s VLM engine immediately reads the often-distorted or handwritten textual content to extract the consignee, cargo IDs, and supply timestamps.
- This knowledge is validated in opposition to the TMS in real-time.
- The system mechanically updates the cargo standing to delivered, which concurrently triggers an bill to be despatched to the shopper and updates the customer-facing monitoring portal.
The end result: This workflow accelerates billing cycles from days to minutes, reduces disputes over supply instances, and supplies the real-time provide chain visibility that prospects now count on.
c. Insurance coverage and Healthcare
This sector is burdened by complicated, standardized varieties which can be crucial for affected person care and income cycles.
The method earlier than IDP: Workers at a clinic manually transcribe affected person knowledge from registration varieties and medical declare varieties (just like the CMS-1500 within the US) into an Digital Well being File (EHR) system. This gradual course of introduces a major danger of information entry errors that may result in declare denials or, worse, have an effect on affected person care.
The workflow with Clever Knowledge Seize:
- Scanned affected person varieties or digital PDFs of claims are ingested by the IDP system.
- The platform precisely extracts affected person demographics, insurance coverage coverage numbers, prognosis codes (e.g., ICD-10), and process codes.
- The system mechanically validates the information for completeness and might test coverage info in opposition to an insurer’s database by way of an API.
- Verified knowledge is then seamlessly pushed into the EHR or a claims adjudication workflow.
The end result: The end result of this automated workflow is a major discount in guide intervention and operational price. In response to McKinsey’s Finest-in-class digital doc processing: A payer perspective report, main healthcare payers use this sort of an strategy to automate 80 to 90 p.c of their claims consumption course of. This resulted in a discount of guide touchpoints by greater than half and cuts the fee per declare by 30 to 40 p.c. That is validated by suppliers like Outlined Bodily Remedy, which automated its CMS-1500 type processing with Nanonets and lowered its declare processing time by 85%.
The strategic playbook: Implementation and future outlook
Understanding the know-how and its worth is step one. The following is placing that data into motion. A profitable implementation requires a clear-eyed view of the challenges, a sensible plan, and an understanding of the place the know-how is headed.
Overcoming the implementation hurdles
Earlier than starting an implementation, it is important to acknowledge the first obstacles that trigger automation initiatives to fail.
- The info high quality hurdle: That is probably the most important problem. As established in AIIM’s 2024 report, the first barrier to profitable AI initiatives is the standard of the underlying knowledge. The primary points are knowledge silos, redundant info, and an absence of information standardization throughout the enterprise. An IDP mission have to be seen as an information high quality initiative at first.
- The organizational hurdle: The identical AIIM report highlights a major abilities hole inside most organizations, significantly in areas like AI governance and workflow course of design. This underscores the worth of adopting a managed IDP platform that doesn’t require an in-house staff of AI consultants to configure and preserve.
- The mixing hurdle: With the typical group utilizing greater than 10 totally different info administration programs, making a seamless move of information is a serious problem. A profitable knowledge seize technique should prioritize options with strong, versatile APIs and pre-built connectors to bridge these system gaps.
A sensible plan for implementation
A profitable IDP implementation doesn’t require an enormous bang strategy. A phased, methodical rollout that proves worth at every stage is the simplest means to make sure success and stakeholder buy-in.
Part 1: Begin small with a high-impact pilot
As an alternative of trying to automate each doc course of without delay, choose a single, high-pain, high-volume workflow. For many organizations, that is AP bill processing. Step one is to determine a transparent baseline: calculate your present common price and processing time for a single doc in that workflow.
Part 2: Validate with a no-risk take a look at
De-risk the mission by proving the know-how’s accuracy in your particular paperwork earlier than making a major funding. Collect 20-30 real-world examples of your chosen doc sort, ensuring to incorporate the messy, low-quality scans and strange codecs. Use an IDP platform that provides a free trial to check its out-of-the-box efficiency on these information.
Part 3: Map the total workflow
Knowledge extraction is just one piece of the puzzle. To attain true automation, it’s essential to map the whole course of from doc arrival to its remaining vacation spot. This includes configuring the 2 most crucial elements of an IDP platform:
- Validation guidelines: Outline the enterprise logic that ensures knowledge high quality (e.g., matching a PO quantity to your ERP knowledge).
- Integrations: Arrange the connectors that can mechanically ship the clear knowledge to downstream programs.
Part 4: Measure and scale
As soon as your pilot workflow is stay, observe its efficiency in opposition to your preliminary baseline. The important thing metrics to observe are Accuracy Charge, Processing Time per Doc, and STP Charge (the share of paperwork processed with no human intervention). The confirmed ROI from this primary course of can then be used to construct the enterprise case for scaling the answer to different doc sorts and departments.
The longer term outlook: What’s subsequent for knowledge seize
The sector of clever knowledge seize continues to evolve quickly. As of August 2025, three key developments are shaping the way forward for the know-how:
- Generative AI and RAG: The first driver for the way forward for knowledge seize is its position because the important gasoline for Generative AI. As extra corporations construct inner RAG programs to permit staff and prospects to “ask questions of their knowledge,” the demand for high-quality, structured info extracted from paperwork will solely intensify.
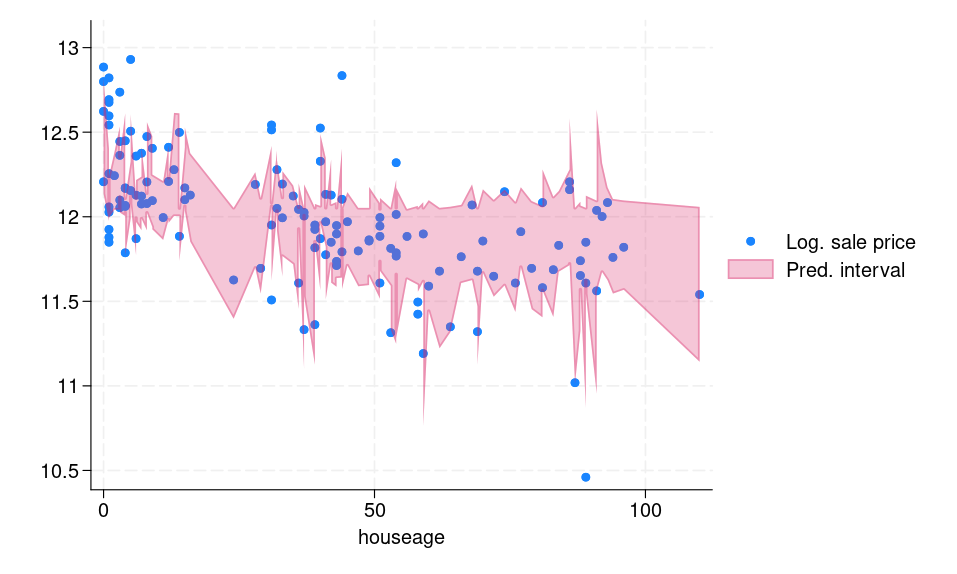
- Multimodal AI: The know-how is transferring past simply textual content. As detailed within the Doc Parsing Unveiled analysis paper, the following technology of IDP is powered by superior VLMs that may perceive and extract info from photographs, charts, and tables inside a doc and clarify their relationship to the encircling textual content.
- Agentic AI: This represents the following frontier, the place AI strikes from being a software that responds to a system that acts. In response to a 2025 PwC report, these AI brokers are designed to automate complicated, multi-step workflows autonomously. For instance, an AP agent could possibly be tasked with resolving an bill discrepancy. It will then independently retrieve the bill and PO, examine them, determine the mismatch, draft a clarification e-mail to the seller, and create a follow-up activity within the applicable system.
Conclusion: From a secular activity to a strategic enabler
Clever knowledge seize is not a easy digitization activity; it’s the foundational layer for the fashionable, AI-powered enterprise. The know-how has advanced from brittle, template-based OCR to clever, context-aware programs that may deal with the complexity and variety of real-world enterprise paperwork with verifiable accuracy and a transparent return on funding.
By fixing the enter downside, clever knowledge seize breaks down the data silos which have lengthy plagued companies, remodeling unstructured knowledge from a legal responsibility right into a strategic asset. For the pragmatic and skeptical professionals on the entrance traces of doc processing, the guarantees of automation are lastly changing into a sensible actuality.
Your subsequent steps
- Calculate your price of inaction. Establish your single most painful doc course of. Use the trade common of $17.61 per manually processed bill as a place to begin and calculate your present month-to-month price. That is the finances you’re already spending on inefficiency.
- Run a 15-minute accuracy take a look at. Collect 10 various examples of that downside doc. Use a free trial of an IDP platform to see what stage of accuracy you’ll be able to obtain by yourself information in minutes, with none customized coaching.
- Whiteboard one end-to-end workflow. Map the whole journey of a single doc, from its arrival in an e-mail inbox to its knowledge being usable in your ERP or accounting system. Each guide touchpoint you determine is a goal for automation. This map is your blueprint for reaching true straight-through processing.
FAQs
What’s the distinction between knowledge seize and OCR?
Optical Character Recognition (OCR) is a particular know-how that converts photographs of textual content into machine-readable characters. It’s a single, foundational part of a bigger course of.
Knowledge Seize (or extra precisely, Clever Doc Processing) is the entire, end-to-end enterprise workflow. This workflow contains ingestion, pre-processing, classification, knowledge extraction (which makes use of OCR as one among its instruments), automated validation in opposition to enterprise guidelines, and eventually, integration into different enterprise programs.
How does clever knowledge seize guarantee knowledge accuracy?
Clever knowledge seize makes use of a multi-layered strategy to make sure accuracy far past what easy OCR can present:
Contextual AI Extraction: Using VLMs permits the system to know the doc’s context, decreasing the chance of misinterpreting fields (e.g., complicated a “due date” with an “bill date”).
Confidence Scoring: The AI assigns a confidence rating to every extracted discipline, mechanically flagging low-confidence knowledge for human evaluation.
Automated Validation Guidelines: The system mechanically checks the extracted knowledge in opposition to your particular enterprise logic (e.g., confirming that subtotal + tax = whole quantity).
Database Matching: It could validate knowledge in opposition to exterior databases, resembling matching a purchase order order quantity on an bill in opposition to a listing of open POs in your ERP system.
What’s one of the best ways to seize knowledge from handwritten varieties?
One of the simplest ways to seize knowledge from handwritten varieties is to make use of a contemporary IDP answer powered by superior AI and multimodal Giant Language Fashions (LLMs). Whereas older know-how referred to as Clever Character Recognition (ICR) was used for this, a 2024 analysis paper titled Unlocking the Archives discovered that fashionable LLMs obtain state-of-the-art accuracy on handwritten textual content out-of-the-box. They’re 50 instances quicker and 1/fiftieth the price of specialised legacy software program, and they don’t require the impractical step of being educated on a particular individual’s handwriting to be efficient.
How do you calculate the ROI of automating knowledge seize?
The ROI is calculated by evaluating the overall price of your guide course of to the overall price of the automated course of. A easy framework is:
Calculate Your Handbook Price: Decide your price per doc (Time per doc x Worker hourly price) + Prices of fixing errors. A broadly used trade benchmark for a single bill is $17.61.
Calculate Your Automated Price: This contains the software program subscription charge plus the price of labor for dealing with the small share of exceptions flagged for guide evaluation. The benchmark for a totally automated bill is beneath $2.70.
Decide Month-to-month Financial savings: Whole Month-to-month Handbook Price – Whole Month-to-month Automated Price.
Calculate Payback Interval: Whole Upfront Implementation Price / Month-to-month Financial savings.
Can knowledge seize software program combine with ERP programs like SAP or NetSuite?
Sure. Seamless integration with Enterprise Useful resource Planning (ERP) and accounting programs is a crucial characteristic of any fashionable knowledge seize platform. That is important for reaching true end-to-end automation for processes like accounts payable. Main IDP options supply a mixture of pre-built connectors for fashionable programs like SAP, NetSuite, QuickBooks, and Xero, in addition to versatile APIs for customized integrations. This enables the clear, validated knowledge to move immediately into your system of document with none guide re-entry.
How does automated knowledge seize assist with GDPR and CCPA compliance?
Automated knowledge seize helps with compliance for laws like GDPR (within the EU) and CCPA (within the US) in a number of key methods:
Creates a Clear Audit Path: The system supplies an immutable digital log of each doc that’s processed, displaying what knowledge was accessed, by whom, and when. That is important for accountability.
Permits Knowledge Minimization: Platforms might be configured to solely extract mandatory knowledge fields and might mechanically redact or masks delicate Personally Identifiable Info (PII).
Strengthens Entry Management: Not like paper paperwork, digital knowledge might be protected with strict, role-based entry controls, guaranteeing that solely licensed personnel can view delicate info.
Supplies Safe Storage and Deletion: The info is dealt with in safe, encrypted environments, and platforms can implement knowledge retention insurance policies to mechanically delete knowledge in line with regulatory necessities.